And how did GSA obtain vulnerability information such as CVES? It seems like vulnerability tables doesnot have.
Hi,
Vulnerability Tests (VTs) are referencing CVE IDs. The CVE information for the CVE IDs is provided by the SCAP data feed. The data itself is provided as XML documents and can be found at the /var/lib/gvm/scap-data/ directory.
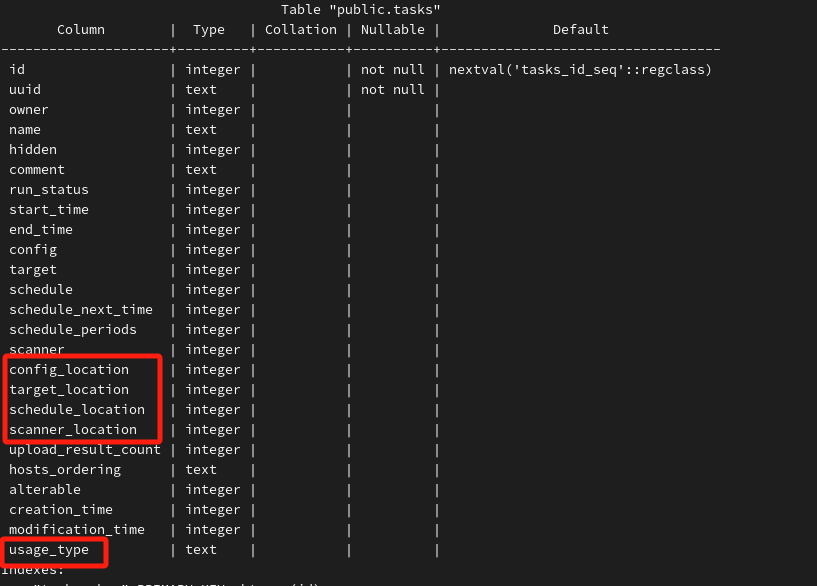
- What does the word “location” in the task table mean. Is there any other value for usage_type in the task table besides scanning.
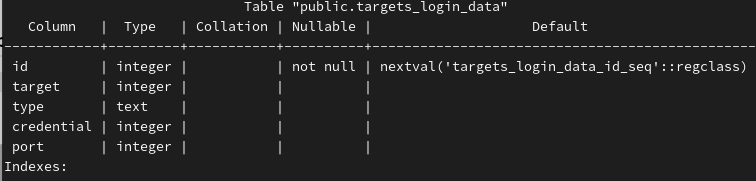
- Why is the credentials table not associated with hosts, but with targets? Are the hosts in the targets trying to authenticate one by one?
Hi CZX,
From your recent questions, I guess you will most easily find answers by inspecting the source code of the Greenbone components. While we strive to help community members solve their usability issues and accept any bugs reported here, it is difficult for us to spend lots of time answering questions about how various components behave. Especially since the Greenbone products are open-source, the code is there for you to inspect and support your own learning curve. ![]()
It seems that it also possible to create documentation on the database schema on your own: