Hi Greenbone Community,
I doesn,t know what’s wrong with this, here take a look at my setup, its a fresh setup
──(chanbasha㉿kali)-[~]
└─$ sudo gvm-setup
[sudo] password for chanbasha:
[>] Starting PostgreSQL service
[>] Creating GVM’s certificate files
[>] Creating PostgreSQL database
[i] User _gvm already exists in PostgreSQL
[i] Database gvmd already exists in PostgreSQL
[i] Role DBA already exists in PostgreSQL
[] Applying permissions
NOTICE: role “_gvm” has already been granted membership in role “dba” by role “postgres”
GRANT ROLE
[i] Extension uuid-ossp already exists for gvmd database
[i] Extension pgcrypto already exists for gvmd database
[i] Extension pg-gvm already exists for gvmd database
[>] Migrating database
[>] Checking for GVM admin user
[] Configure Feed Import Owner
[*] Update GVM feeds
Running as root. Switching to user ‘_gvm’ and group ‘_gvm’.
Trying to acquire lock on /var/lib/openvas/feed-update.lock
Acquired lock on /var/lib/openvas/feed-update.lock
⠧ Downloading Notus files from
rsync://feed.community.greenbone.net/community/vulnerability-feed/22.04/vt-da
ta/notus/ to /var/lib/notus
⠏ Downloading NASL files from
rsync://feed.community.greenbone.net/community/vulnerability-feed/22.04/vt-da
ta/nasl/ to /var/lib/openvas/plugins
Releasing lock on /var/lib/openvas/feed-update.lock
Trying to acquire lock on /var/lib/gvm/feed-update.lock
Acquired lock on /var/lib/gvm/feed-update.lock
⠙ Downloading SCAP data from
rsync://feed.community.greenbone.net/community/vulnerability-feed/22.04/scap-
data/ to /var/lib/gvm/scap-data
⠙ Downloading CERT-Bund data from
rsync://feed.community.greenbone.net/community/vulnerability-feed/22.04/cert-
data/ to /var/lib/gvm/cert-data
⠴ Downloading gvmd data from
rsync://feed.community.greenbone.net/community/data-feed/22.04/ to
/var/lib/gvm/data-objects/gvmd/22.04
Releasing lock on /var/lib/gvm/feed-update.lock
[*] Checking Default scanner
08b69003-5fc2-4037-a479-93b440211c73 OpenVAS /run/ospd/ospd.sock 0 OpenVAS Default
[i] No need to alter default scanner
[+] Done
[i] Admin user already exists for GVM
[i] If you have forgotten it, you can change it. See gvmd manpage for more information
[>] You can now run gvm-check-setup to make sure everything is correctly configured
┌──(chanbasha㉿kali)-[~]
└─$ sudo gvm-check-setup
gvm-check-setup 23.11.0
Test completeness and readiness of GVM-23.11.0
Step 1: Checking OpenVAS (Scanner)…
OK: OpenVAS Scanner is present in version 23.13.1.
OK: Notus Scanner is present in version 22.6.4.
OK: Server CA Certificate is present as /var/lib/gvm/CA/servercert.pem.
Checking permissions of /var/lib/openvas/gnupg/*
OK: _gvm owns all files in /var/lib/openvas/gnupg
OK: redis-server is present.
OK: scanner (db_address setting) is configured properly using the redis-server socket: /var/run/redis-openvas/redis-server.sock
OK: the mqtt_server_uri is defined in /etc/openvas/openvas.conf
OK: _gvm owns all files in /var/lib/openvas/plugins
OK: NVT collection in /var/lib/openvas/plugins contains 93567 NVTs.
OK: The notus directory /var/lib/notus/products contains 495 NVTs.
Checking that the obsolete redis database has been removed
Could not connect to Redis at /var/run/redis-openvas/redis-server.sock: No such file or directory
OK: No old Redis DB
Starting ospd-openvas service
Waiting for ospd-openvas service
OK: ospd-openvas service is active.
OK: ospd-OpenVAS is present in version 22.7.1.
Step 2: Checking GVMD Manager …
OK: GVM Manager (gvmd) is present in version 24.0.0.
Step 3: Checking Certificates …
OK: GVM client certificate is valid and present as /var/lib/gvm/CA/clientcert.pem.
OK: Your GVM certificate infrastructure passed validation.
Step 4: Checking data …
OK: SCAP data found in /var/lib/gvm/scap-data.
OK: CERT data found in /var/lib/gvm/cert-data.
Step 5: Checking Postgresql DB and user …
OK: Postgresql version and default port are OK.
gvmd | _gvm | UTF8 | libc | en_IN | en_IN | | |
16436|pg-gvm|10|2200|f|22.6||
OK: At least one user exists.
Step 6: Checking Greenbone Security Assistant (GSA) …
OK: Greenbone Security Assistant is present in version 24.0.0~git.
Step 7: Checking if GVM services are up and running …
Starting gvmd service
Waiting for gvmd service
OK: gvmd service is active.
Starting gsad service
Waiting for gsad service
OK: gsad service is active.
Step 8: Checking few other requirements…
OK: nmap is present.
OK: ssh-keygen found, LSC credential generation for GNU/Linux targets is likely to work.
OK: nsis found, LSC credential package generation for Microsoft Windows targets is likely to work.
OK: xsltproc found.
WARNING: Your password policy is empty.
SUGGEST: Edit the /etc/gvm/pwpolicy.conf file to set a password policy.
Step 9: Checking greenbone-security-assistant…
OK: greenbone-security-assistant is installed
It seems like your GVM-23.11.0 installation is OK.
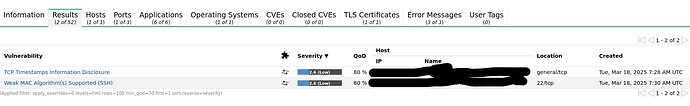
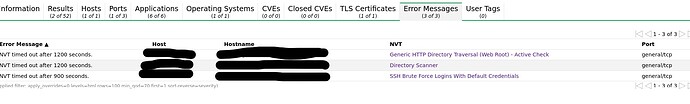
When I run a scan which the target(Linux) allows the ICMP ping with Scan default and IANA assigned TCP with unauthenticated scan with updated current feed
Even through the target machine has many ports running services, It doesn’t shows any vulnerabilities and the ports services. (also tried with consider alive)
I have tried the scans for other machines too, it shows only the 2.6 (Low) - Severity all the target even though it has many ports running services.
Let me know if further information is needed to resolve my issue.
Kindly help me to find the vulnerabilities based on the severity level.
Thanks,