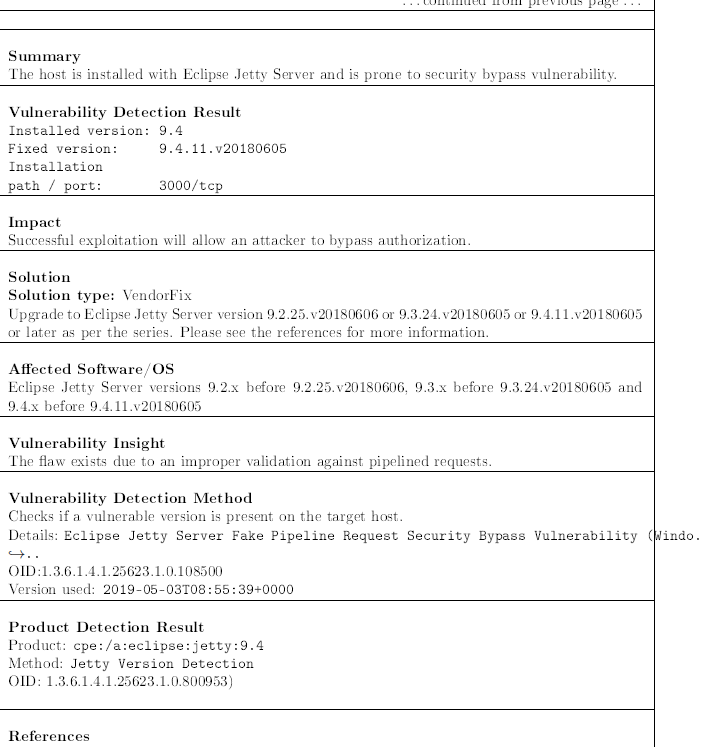
[Eclipse Jetty Server Fake Pipeline Request Security Bypass Vulnerability (Windows)
we are getting this issue and as we checked with eclipse community they told us that there is no issue in there jetty sever
after update also we are getting the same issue
they are telling us that there is bug in openvas
so please give us the resolution for this
Thanks for your report. Could you please answer a few questions:
- Which version of Jetty are you running?
- Which operating system is used as the host for the Jetty service?
- Why do you think that this is not reported correctly?
- Which output are you getting in the mentioned VT?
- jetty version 9.4
- windows server 2008 r2 standard edition 64 bit
- everytime we get the same issue after upgarding the jetty server
- we are getting that to update the jetty server
Could you please post the output of the VT? It should give you a hint which version you have currently installed and if you have updated the version correctly (e.g. your server might still run the outdated Jetty version if the update failed for example).
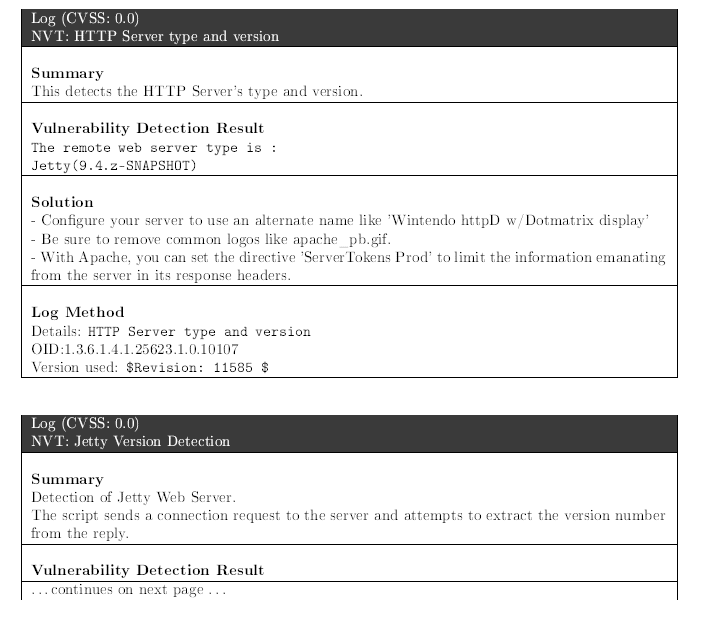
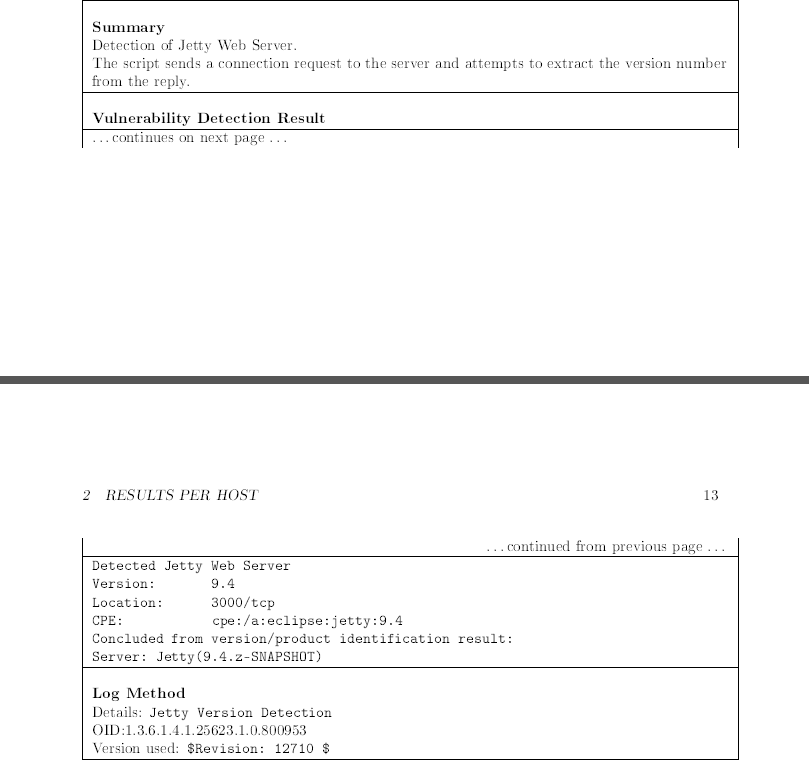
Thanks again, this makes things more clear. Could you please also post the output of the VT “Jetty Version Detection” (OID: 1.3.6.1.4.1.25623.1.0.800953)? You might need to show “log level” entries in your report.
Basically it seems your Jetty Server is providing / using an uncommon version scheme not matching whats usually exposed (e.g. 9.4.10.v20180503).
Thanks again for providing this issue. Indeed the previously assumption was right:
as the version is exposed like 9.4.z-SNAPSHOT where only version 9.4 was extracted the mentioned VT has assumed this as version 9.4.0 and reported it as vulnerable because 9.4.0 < 9.4.11.v20180605.
This has been addressed today and should be shipped in the feed in the next few days.
Okay so in the next feed hope the issue got resolve.
Thanks