Hi there,
with our IT team we performed some Vulnerability Assessment scans thanks to Greenbone Source Edition and the OpenVAS Scanner.
Specifically, for testing, we ran a first scan to a single target: a QNAP ts-x53u model.
The results showed us that OpenVAS Scanner has found the following CPE: cpe:/h:qnap:ts-x53u:5.0.0_20211221
The model and the product version are the right ones. But we have some doubts around this CPE because we tried to search in the NIST Official site, with no results.
After a research in the Greenbone Community Portal, we found this thread.
So, we got that OpenVAS Scanner utilize “.nasl” scripts to perform detection of version and product of the targets, which in our case it is a qnap ts-x53u with QTS 5.0.0.
From this, we assume that OpenVAS Scanner generates it’s own CPEs with this .nasl scripts.
Questions:
- Is it true that OpenVAS uses .nasl scripts to get product model and version of the target?
- Is it true that OpenVAS generates it’s own CPEs thanks to the infos gathered through these scripts? If yes, how? If no, can you explain how OpenVAS handles CPEs?
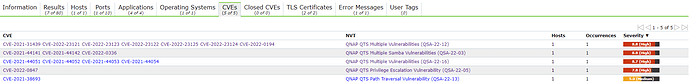
We saw that for the cpe:/h:qnap:ts-x53u:5.0.0_20211221, OpenVAS has found some CVEs:
Last questions: How OpenVAS can address those CVEs if it uses a CPE that is not present on NIST database? Which is the process behind the link between the CPE generated (cpe:/h:qnap:ts-x53u:5.0.0_20211221) and the CVEs discovered and assigned to it?
Thanks!